 You hear about hacks all the time in the news. Major websites have had data leaks and lost their users personal information. Computers get infected and malware saves your login details for bank accounts and credit cards. In the worst cases, identity theft occurs because it is an easy crime to commit and has a high reward.
You hear about hacks all the time in the news. Major websites have had data leaks and lost their users personal information. Computers get infected and malware saves your login details for bank accounts and credit cards. In the worst cases, identity theft occurs because it is an easy crime to commit and has a high reward.
In the past, passwords could be used to keep the bad guys out of your accounts but a single form of authentication is not enough anymore. Cyber hackers have a variety of methods including phishing, pharming and keylogging to steal your password. Also togdays computers have the power to test billions of password combinations.
To make things worse the majority of people use the same password for several websites. That means anybody who has figured out that password has access to multiple accounts that you own. In a time when it is extremely easy to look up what a persons pet is called or their maiden name is, security questions aren’t much help.
Consider how a bank operates. They don’t simply keep their valuables locked away with one key. There are alarms ready to be triggered, motion detectors and even bars on the windows. Your data is valuable and you need more than one line of defense to protect it.
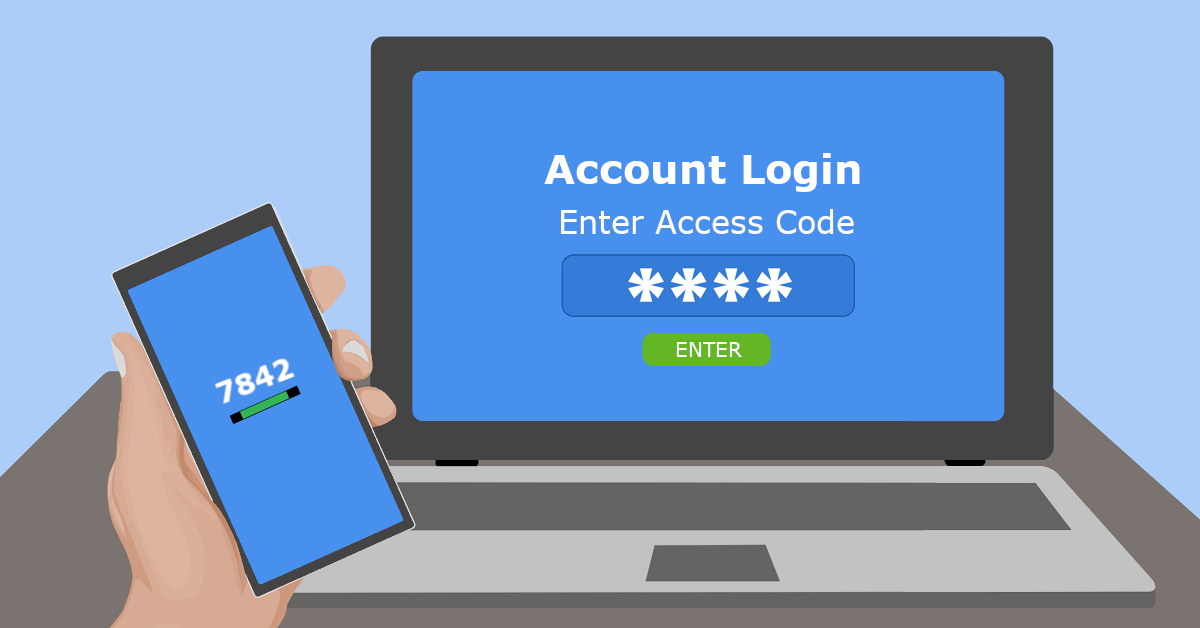
In the computer world, your second line of defense (after your username and password combination) is called “2-factor authentication” (2FA). Sometimes it is referred to as multiple-step or multi-factor verification (MFA). 2-factor authentication is a way to double check a person’s identity. This can be enabled every time a person logs in or just under certain circumstances. For example, signing in from a new device or different country might trigger 2-factor authentication.
Many of the services you may already use, such as Facebook, Gmail, Office365, Xero Accounting, and more, have 2-factor authentication options. If your bank has ever sent you a special code through text or email to enter before logging in, you have already used a type of 2-factor authentication. They can also be in the form of a app on your phone or a small electronic dongle.
MFA is absolutely crucial for online banking, email, and online shopping such as Amazon or PayPal. It’s also a must-have for cloud storage accounts (like Dropbox or Sync), password managers, communications apps, and productivity apps. This is especially true if you frequently use the same passwords for different websites and apps.
Some may consider MFA unnecessary for social networks accounts, but these are actually very important to keep safe. For ease, a lot of websites and apps allow you to sign up through your Facebook or Twitter account. You need to keep these networks safe so that somebody with your password can not suddenly get into every account you have linked.
The point of using MFA is to make hackers’ lives harder and prevent them from easily getting into your accounts. If they have captured your login username and password, they still need a second method to get in, especially when the computer or phone they are using has never logged into your account before. This makes it much harder for anybody to breach your account.
Plus, if you receive a notification with a special code to enter for logging in (and you weren’t trying to log into that account), you have a good signal that somebody else was trying to get in. That means it’s time to change that password and be grateful you had MFA configured.
It is unfortunate that there is currently an abundance of skilled hackers ready to take advantage of those unprepared. Luckily, you can still stop them – even if they have your login information at hand. MFA is one of the easiest methods to keep your accounts safe.
Give us a call at (08) 8326 4364 or via email on
su*****@dp*********.au
to help secure your business and accounts.

Pingback: 8 Cyber Security Tips To Help Secure Your Business | DP Computing's Blog
Pingback: What to Do If Your Data Is Included in a Leak | DP Computing's Blog
Pingback: Don’t Change Your Password! | DP Computing's Blog
Pingback: Why You Shouldn’t Use SMS as your 2FA | DP Computing's Blog
Pingback: 5 Security Vulnerabilities You Need To Fix ASAP | DP Computing's Blog
Pingback: What form of MFA Is The Best? | DP Computing's Blog